Not a Hack. A Handout. Inside the GTFOice.org Data Exposure
Built with vibes, secured by nothing, and somehow surprised when the data walked out the door
People signed up to stop ICE, expecting to be connected with tools and guidance to help organize against detention facilities in their communities. Instead, what they appear to have received was something far more concerning: their personal information left exposed in a way that required little effort to access, followed by a message that immediately raised alarm.
Over the weekend, we reported that something was wrong with GTFOICE.org, a high-profile anti-ICE organizing site associated with Miles Taylor, who previously served as Chief of Staff at the Department of Homeland Security, the same agency that oversees ICE. The project is described as a collaboration between DEFIANCE.org, Project Salt Box, and Save America Movement.
At first glance, the situation looked like a potential data breach. However, as we began to dig deeper, the picture that emerged was not one of a sophisticated hack, but of a system that may never have had meaningful protections in place to begin with.
Nearly 18,000 people entered their personal information into the platform, including names, email addresses, phone numbers, and zip codes with the expectation that they would receive a playbook or be connected to local organizing efforts. Instead, that data appears to have been accessible through a publicly exposed API that lacked basic safeguards, such as authentication and rate limiting, meaning that anyone who knew where to look could potentially view and collect large amounts of sensitive information tied to anti-ICE organizing activity.
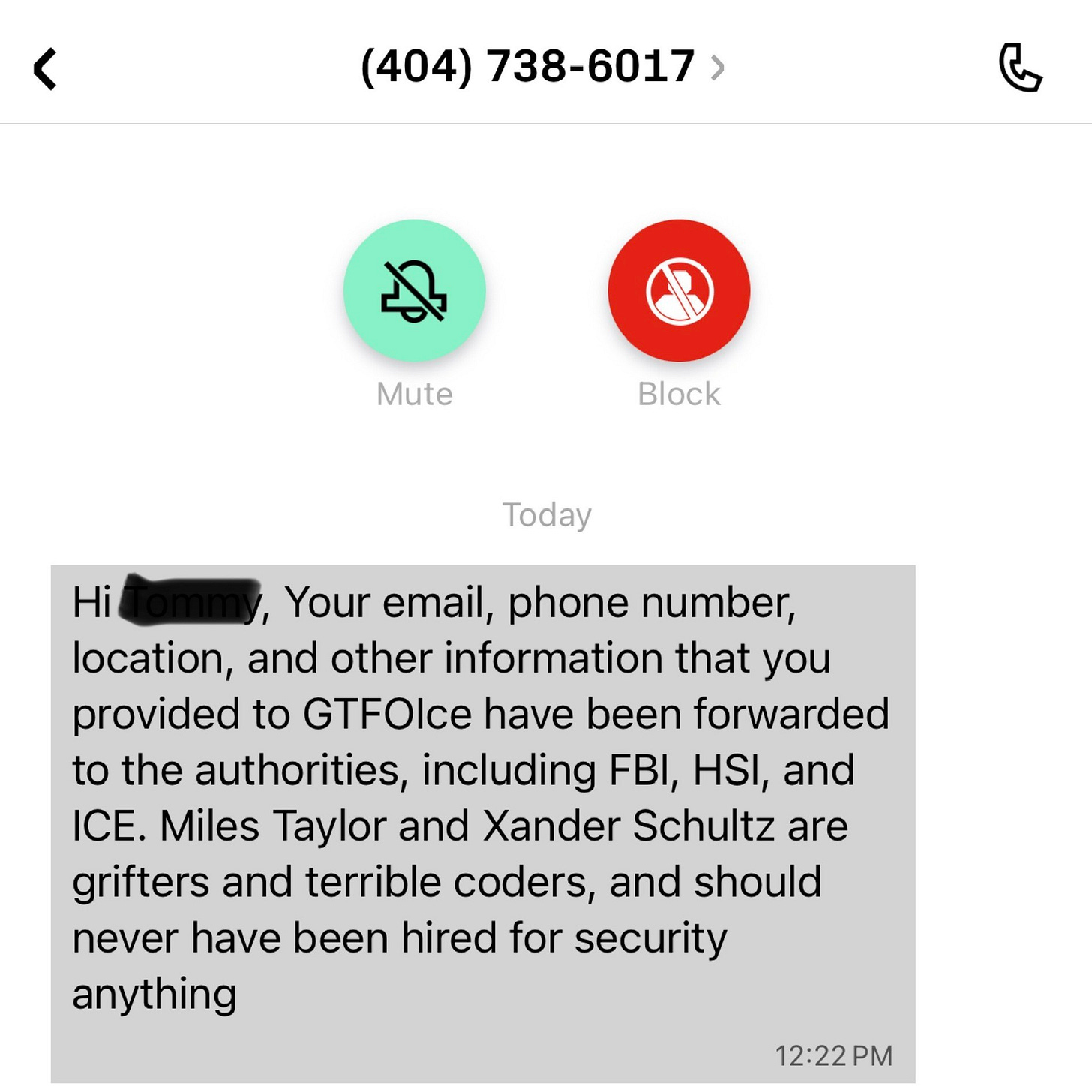
The situation escalated further when members of our team, who had signed up across multiple locations using different phone numbers, received the following message days later:
“Hi *****, Your email, phone number, location, and other information that you provided to GTFOIce have been forwarded to the authorities, including FBI, HSI, and ICE. Miles Taylor and Xander Schultz are grifters and terrible coders, and should never have been hired for security anything”
We cannot independently verify the claim made in that message, but its impact was immediate, amplifying fears about how exposed this data may have been and who could have accessed it.
In practical terms, this means the data people submitted was effectively sitting out in the open online, without real barriers preventing access and without controls to limit how much could be retrieved. The issue was not that someone broke through layers of security, but that the system itself appears to have made that data available in the first place.
To better understand what actually happened, how serious this exposure may be, and what it reveals about the risks of digital organizing tools, last night I spoke with cybersecurity researcher Scott Petty, a member of the Hagerstown Rapid Response research team, who walked us through his findings and why this situation raises concerns that extend well beyond a single website.
Below, is my interview with Scott Petty, a core member of the Hagerstown Rapid Response research team. Petty is also a Cybersecurity Researcher and Threat Analyst.
McCarthy: What appears to have happened to me regarding the GTFOice data breach is that GTFOice did not take proper security precautions to secure their API and so this hacker / curious person was able to just freely access the personal information. And this lack of basic security measures would appear to be negligence on GTFOice’s part. Scott, you are a cyber security researcher. Is this an accurate description based on what we know so far?
Petty: Correct. I looked into this a bit yesterday and came upon a Twitter post by @DataRepublican. The post contained two redacted screenshots showing a sample of the data that was leaked. At first, I suspected that they had exploited an insecure direct object reference (IDOR) vulnerability, similar to the way Weev leaked AT&T data back in 2010. Upon closer inspection, I noticed that @DataRepublican was using curl, a command line tool for interacting with servers via URLs, and passing “Authorization: Bearer <redacted token>” as a header argument.
McCarthy: So in simpler terms, I think what you are saying is that this wasn’t really a case of someone hacking their way into the GTFOice website? And instead, it looks like they somehow had valid access, and the system just handed over the data.
Petty: Exactly, they may as well have simply added a menu item for their user’s data as they were offering it freely to anyone willing to expend very minimal effort.
But without access to the live site, I can’t say for sure whether this was offered by the server, perhaps upon submitting the sign-up form. However they obtained it, that simple header was all that stood between them and the personally identifiable information of Taylor’s users, including names, email addresses, phone numbers, and zip codes.
McCarthy: So tell me about the second incident.
Petty: Later this afternoon, @DataRepublican announced a similar vulnerability in another of Taylor’s sites, undotrump[.]org, which she and her followers then proceeded to scrape. The screenshots from her post announcing that breach showed that no header was required in this instance, the data was available for the taking by anyone who visited the /api/reservations endpoint. This was confirmed after I found a month-old scan on urlscan.io that included a feed like that disclosed yesterday. The information exposed in today’s incident included names, emails, and messages - some of which were pretty spicy.
McCarthy: Wow, so the users of undotrump[.]org are quite vulnerable too.
Petty: These security lapses are inexcusable and my first thought yesterday when I began looking into this was that someone had probably vibe coded this rubbish, as no competent web developer would be this careless. That suspicion was confirmed when I attempted to visit the site from today’s incident and was met with a Replit 404 “not found” page. Replit is a vibe coding platform and not the sort of thing one should use for a production website, particularly one that was storing potentially sensitive user information.
McCarthy: Yikes, those are strong words! Do you have any advice for people who have had their information compromised from this GTFOice data breach?
Petty: There’s not much you can do once your data’s out there, unfortunately that cat’s already out of the bag. Thankfully, I haven’t seen any evidence that credentials or payment information were leaked and that’s not something that would be typically exposed through the same sort of API endpoint as was scraped. I can offer some suggestions for how people can minimize such threats to their information going forward. To begin with, I recommend using a duck.go email alias, which can be generated on a per site basis, without ever needing to disclose your actual email address to third parties. Anything sent to the alias will be forwarded to the address you configure. Similarly, you can use a VoIP number, such as those offered by Google Voice, instead of giving out your real phone number. There is no need to use your real name unless you’re interacting with the government or making certain financial transactions. Finally, there’s the standard security basics, like using a password manager and a unique password for each site and enabling multi-factor authentication, preferably with a hardware token like a YubiKey.
DEFIANCE.org, Project Salt Box, and Save America Movement asked people to trust them with highly sensitive personal information tied to anti-ICE organizing, telling them “Sign up to tell ICE: Get The Facilities Out at gtfoice.org.” That trust comes with a baseline obligation to protect the people who gave it. Collecting names, phone numbers, and locations without implementing even basic safeguards is not a minor oversight. It is a failure to put the safety of participants first, and that should be the starting point for any accountability moving forward.
Scott’s analysis makes clear this was not a hack in the traditional sense, not to discount the skills of the researchers who discovered the vulnerability. It was a failure to implement even the most basic protections for a dataset that never should have been exposed in the first place.
And that is the real story here. People were not just signing up for a newsletter. They were identifying themselves as part of a movement opposing ICE, often in communities where that carries real risk. That kind of data demands a higher standard of care. Care that it never received.
As more activism moves online, the question is not just who is building these tools, but whether they are capable of handling the responsibility that comes with them.
In this case, the answer appears to be no.
Republishing encouraged. Other outlets are encouraged to republish this article, in full or in part, as long as they clearly credit the original authors and link back to the original source.